The Trump administration, in its first full week in office, moved to restrict how a number of federal agencies communicate with the public, including the media. And while at least some of those restrictions appear to have been loosened, the new administration’s stance on the press is quite clear. “The media here is the opposition party,” chief White House strategist and longtime New York Times reader Steve Bannon said Thursday, adding that the press should “keep its mouth shut” for a while.
The week’s events and the new climate of uncertainty spurred a number of news organizations to remind readers that they are ready and willing to accept leaks, via regular mail and also online with secure tools like SecureDrop, the encrypted anonymous communication software maintained by the Freedom of the Press Foundation.
I wanted to see just how easy it actually was to use SecureDrop, which I’d never done before. I enlisted ProPublica’s help: I told them I’d be sending them a document (a single-page PDF with “This is a test” on it), and asked them to confirm that they received it. This is not what you do if you are actually leaking something and want to remain anonymous, duh, but I was interested to see what things look like on the other side. The full instructions for sources to use SecureDrop are on the SecureDrop website, but essentially, this is what I did — and what you need to do.1. Download the Tor browser here. Install it just as you would install any app on your computer.
2. Open Tor. It’s like using any Internet browser. I was mainly surprised by how slow it is — but that’s a feature, not a bug: “Tor is never going to be blazing fast. Your traffic is bouncing through volunteers’ computers in various parts of the world, and some bottlenecks and network latency will always be present,” Tor explains on its site.
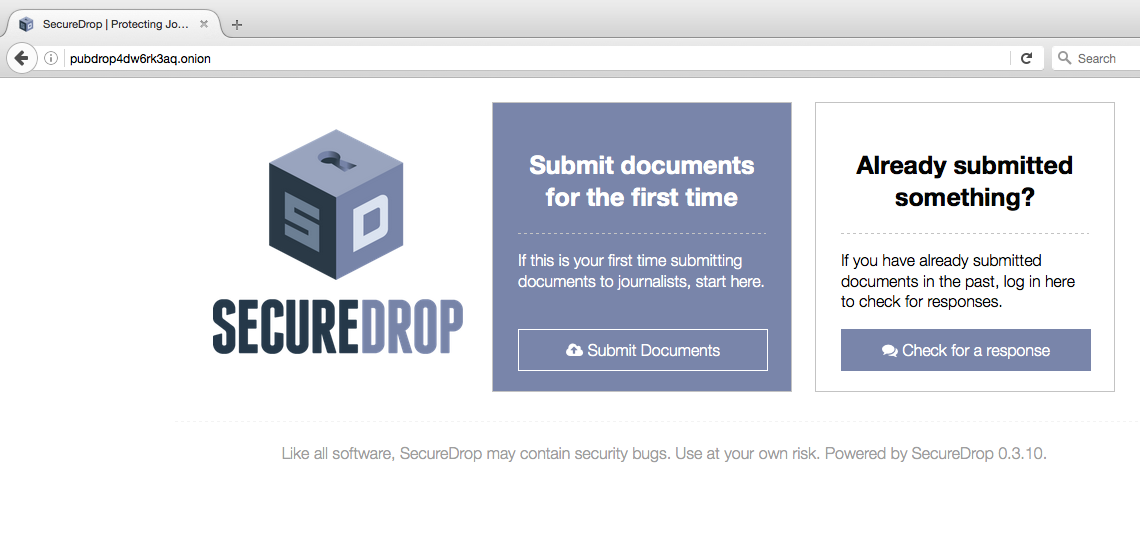
3. Paste the SecureDrop address of the news organization you want to reach (all of these are listed below, ending in .onion) in Tor’s address bar. You’ll see the option to send a document or check the status of one you’ve already sent.
4. You’ll be given a secret codename, which will serve as your login for SecureDrop. Write it down on paper. “The best way to protect your codename is to memorize it,” SecureDrop advises. “If you cannot memorize it right away, we recommend writing it down and keeping it in a safe place at first, and gradually working to memorize it over time. Once you have memorized it, you should destroy the written copy.”
5. Select the file that you want to upload from your computer, or type a message.
6. You can check back for replies to your message by redirecting the Tor browser to the news org’s SecureDrop address and then typing in the secret codename that you wrote down.
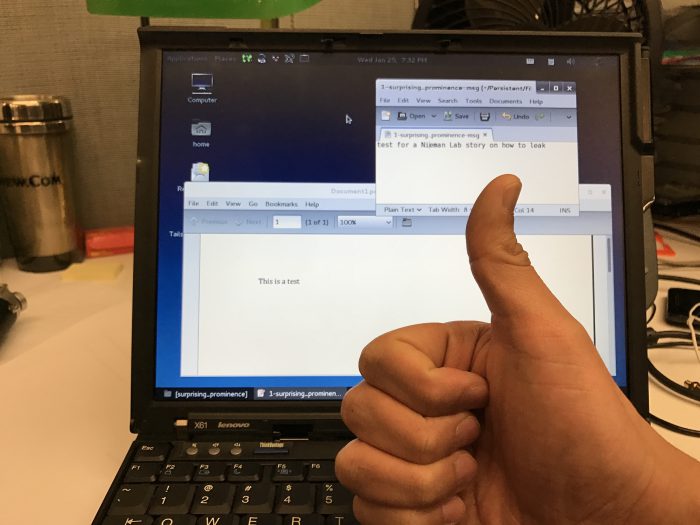
ProPublica’s Mike Tigas confirmed that ProPublica had received my test. Here’s what it looked like on their end — note that ProPublica saw me only as a codename: “surprising prominence.”

I logged back in, using the seven-word codename I’d been assigned in step 4, and saw my response from ProPublica.

That’s it. It was way easier than I thought it would be. Leakers shouldn’t use their work computers and should use public wifi, “like a Starbucks or at a hotel or anywhere where the Internet is open for public use.” And, of course, just using Tor and SecureDrop isn’t a perfect solution for security: If you were doing this from one of your employer’s computers, it might be able to notice that the Tor network was accessed, even if it couldn’t see the contents of whatever you sent. Use as much caution and good sense as you can about distancing yourself from equipment and network locations you might be connected to.
You may also want to watch this video, from Canada’s Globe and Mail, for a visual representation of the above steps.
What follows is a list of news organizations and how to leak to them. The official SecureDrop directory is here, and recommends that you “compare the .onion address provided on the organization’s Landing Page to the corresponding entry in this list, and verify that the addresses match before continuing. This provides a strong layer of defense against certain types of attacks that might try to trick you into visiting a malicious SecureDrop instance masquerading as a legitimate one.”
The Guardian also notes: “We recommend that you don’t jump straight from [the] landing page to the SecureDrop site when uploading, especially on business networks that may be monitored. Best practice would be to make a note of the Tor url and upload your content from a different machine at a later time.”
Leaks landing page [for regular browser]: https://securedrop.propublica.org/
Address in Tor: pubdrop4dw6rk3aq.onion
Mailing address: ProPublica, 155 Avenue of the Americas, 13th floor, New York, NY 10013-1507
Leaks landing page: https://www.nytimes.com/newsgraphics/2016/news-tips/
Address in Tor: nytimes2tsqtnxek.onion
Mailing address: Tips, The New York Times, 620 8th Avenue, New York, NY 10018
WhatsApp and Signal: 1-646-951-4771
Email: tips@nytimes.com, PGP Fingerprint: 44B6 6121 3CE6 66D6 5403 B4CC 44A3 475A E1AA A9EB
Leaks landing page: https://www.washingtonpost.com/securedrop/. See also “Here’s how to leak government documents to The Post.“
Address in Tor: vbmwh445kf3fs2v4.onion
Mailing address: The Washington Post, 1301 K Street NW, Washington DC 20071
Leaks landing page: https://contact.buzzfeed.com/
Address in Tor: 6cws3rcwn7aom44r.onion
Mailing address: BuzzFeed News NY, c/o Mark Schoofs, Investigations & Projects Editor, 111 East 18th Street, BuzzFeed Newsroom, New York, NY 10003
Signal: 1-646-379-1975
Email: investigations@buzzfeed.com, PGP fingerprint: B077 0E9F B742 ED17 B4EF 0CED 72A9 85C4 6203 F09C
Leaks landing page: https://tellontrump.com
Address in Tor: gmg7jl25ony5g7ws.onion
Mailing address: Special Projects Desk, Gizmodo Media Group, 2 West 17th Street, Floor 2, New York, NY 10011
Phone, WhatsApp, Signal: 1-917-999-6143
Leaks landing page: https://www.ap.org/tips/
Address in Tor: 3expgpdnrrzezf7r.onion
Mailing address: The Associated Press, c/o Ted Bridis, investigations editor, 1100 13th Street NW, Suite 500, Washington, DC 20005
Phone, WhatsApp, Signal: 1-202-556-1927
Leaks landing page: https://securedrop.theguardian.com/
Address in Tor: 33y6fjyhs3phzfjj.onion
Mailing address: The Guardian (US Main office), 222 Broadway, 22nd and 23rd Floors, New York, NY 10038
Leaks landing page: http://projects.newyorker.com/strongbox/
Address in Tor: strngbxhwyuu37a3.onion
Mailing address: The New Yorker, 1 World Trade Center, New York, NY 10007
Leaks landing page: https://theintercept.com/leak/
Address in Tor: y6xjgkgwj47us5ca.onion
Mailing address: The Intercept, P.O. Box 65679, Washington, DC 20035 or The Intercept, 114 Fifth Avenue, 18th floor, New York, NY 10011
Leaks landing page: https://news.vice.com/securedrop/
Address in Tor: cxoqh6bd23xa6yiz.onion
Leaks landing page: https://sec.theglobeandmail.com/securedrop/
Address in Tor: n572ltkg4nld3bsz.onion